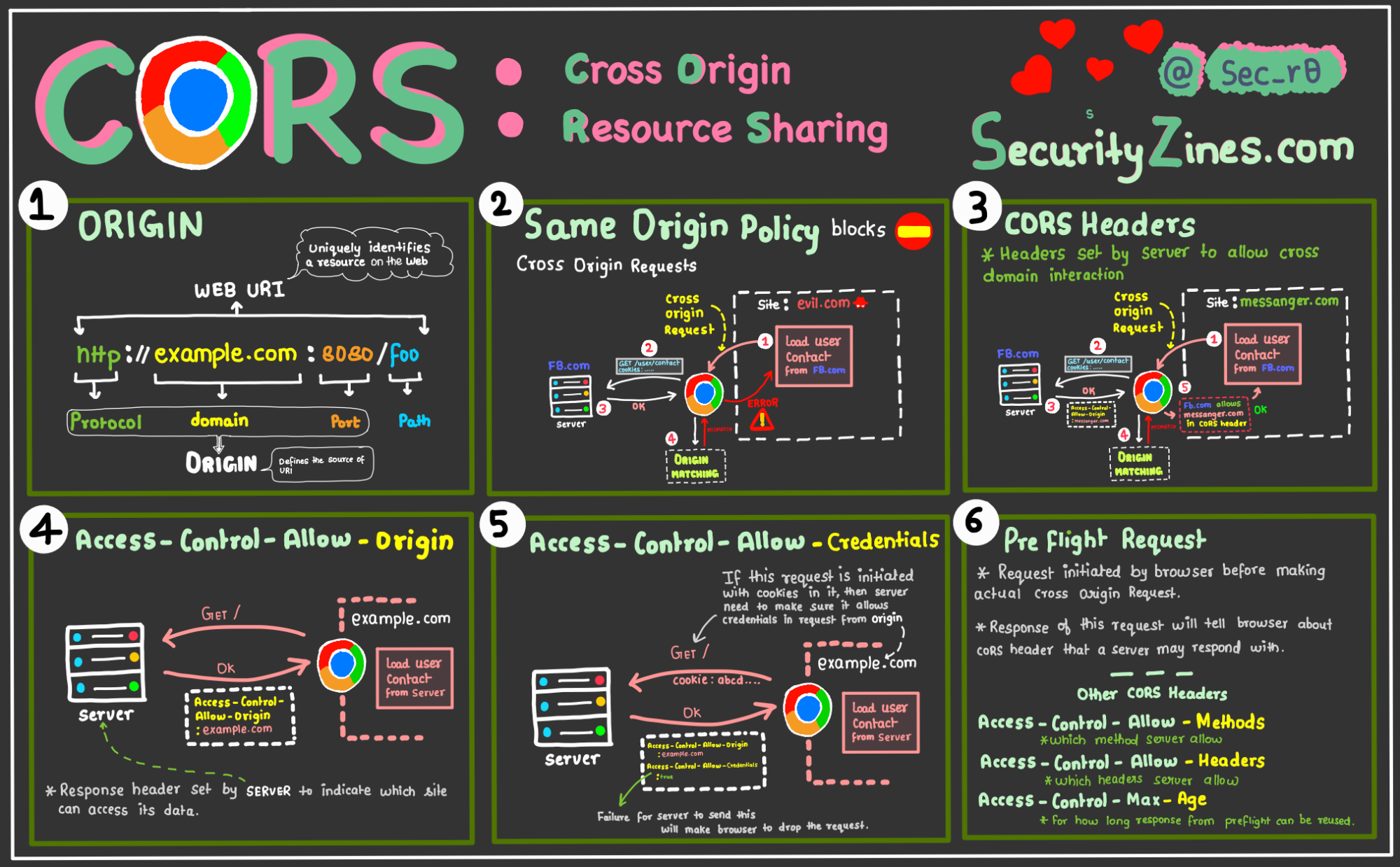
Hack3rScr0lls on X: "We continue to talk about attacks on CORS. This time, we have prepared a set of ideas for bypassing lists of allowed hosts. #CyberSecurity #BugBountyTip #BugBounty https://t.co/o55dRsQjCU" / X
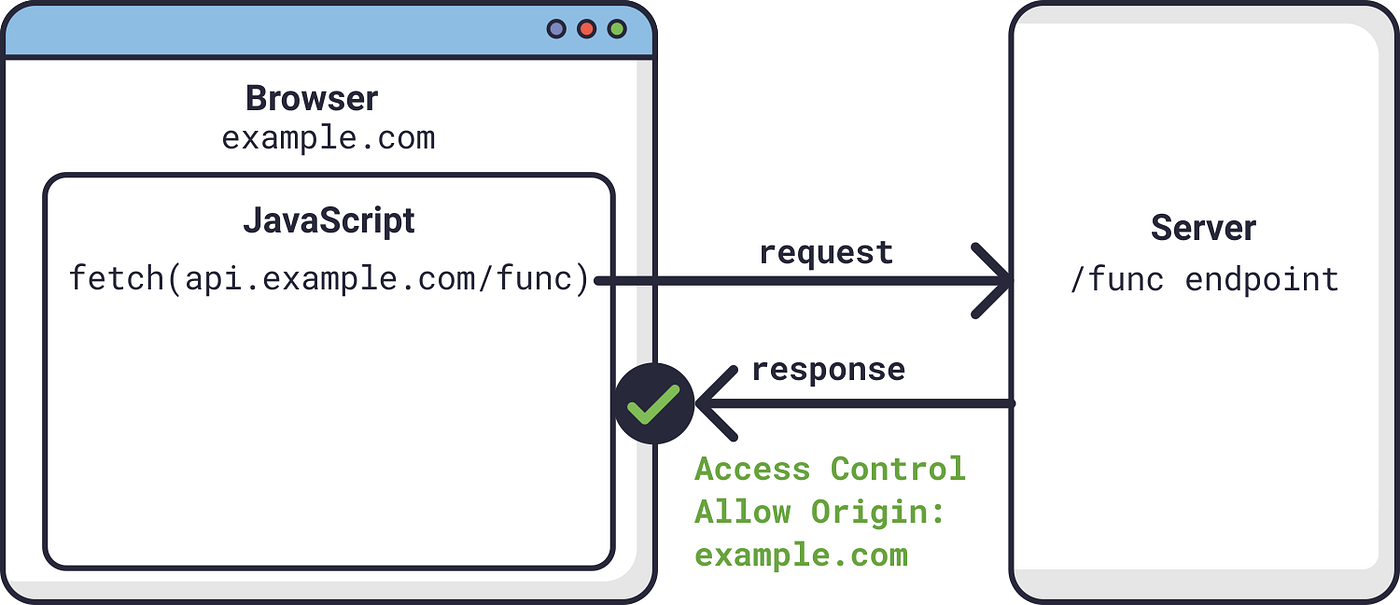
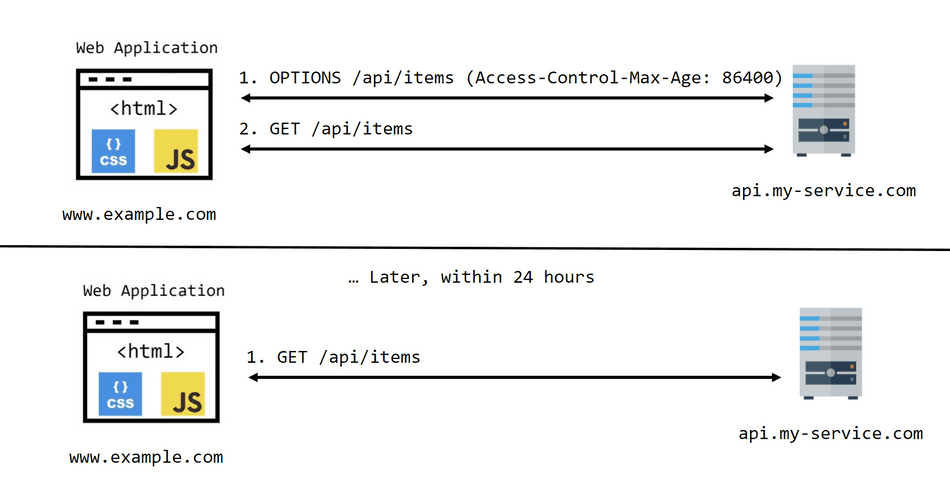
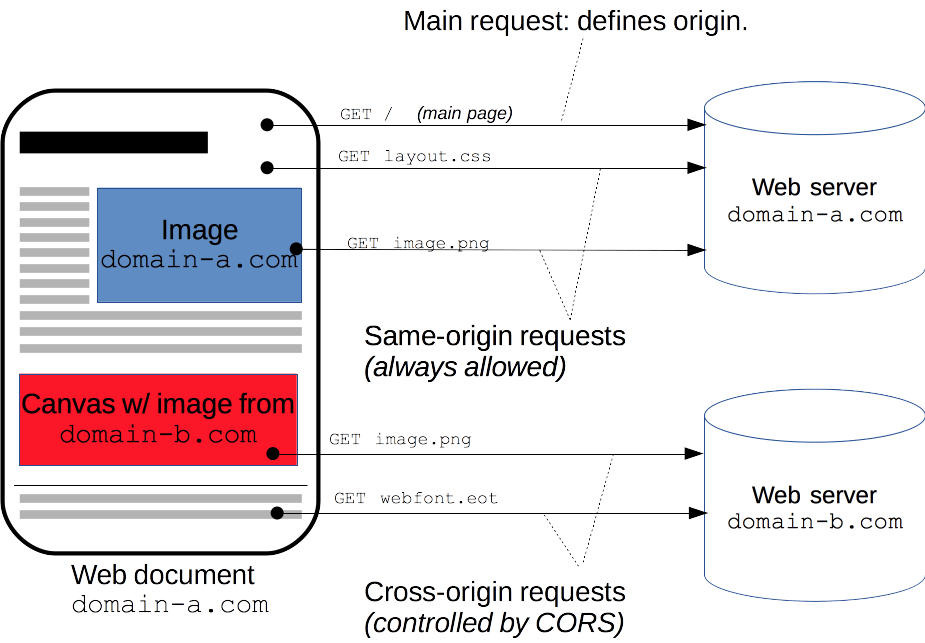
Hacking HTTP CORS from inside out: a theory to practice approach | by Lucas Vinícius da Rosa | InfoSec Write-ups

Bypassing CORS configurations to produce an Account Takeover for Fun and Profit | by Josh Fam | InfoSec Write-ups
Hacking HTTP CORS from inside out: a theory to practice approach | by Lucas Vinícius da Rosa | InfoSec Write-ups

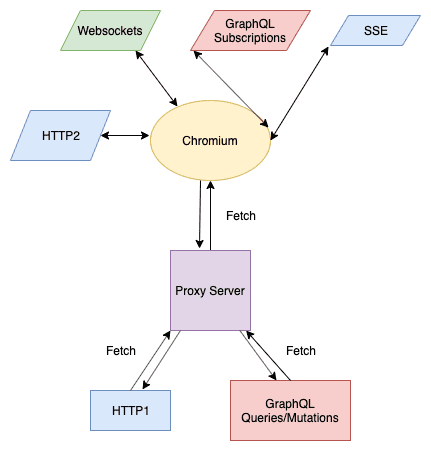
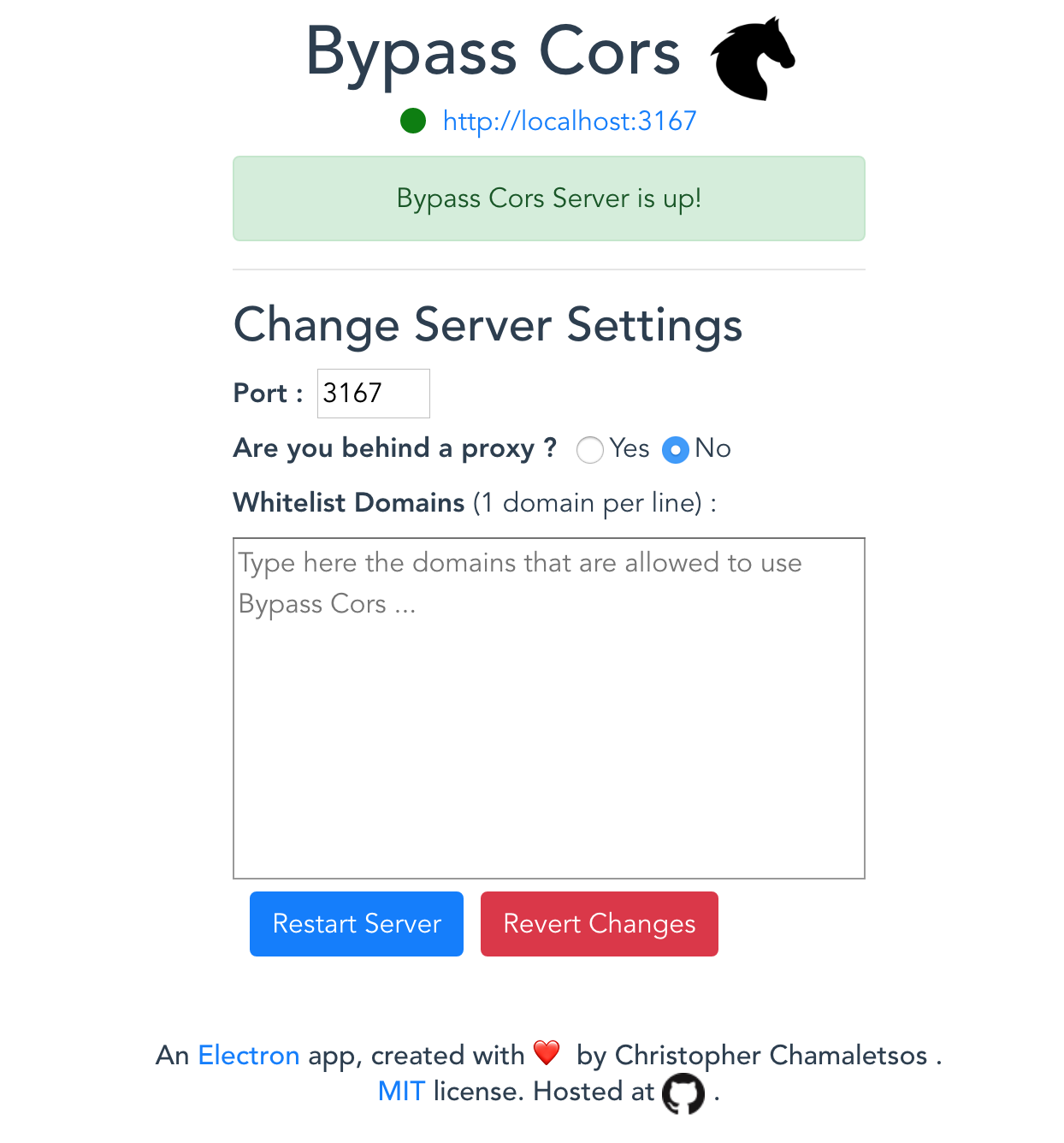
Fixing CORS Errors — How to Build a Proxy Server to Handle Cross-Origin Requests | by Jake McCambley | Medium